How Embedded Intelligence Reduces Compliance Risk Across Accreditation, Clinical Quality Programs, Regulatory Submissions, and Audit
A Perspective from Autonomize AI | 2026
The Compliance Problem Is Structural and the Risks Are Real
Healthcare organizations possess deep regulatory knowledge. What they consistently struggle to build is the operational infrastructure to apply that knowledge reliably, at scale, across every case, every submission, and every audit cycle. That gap between knowing what compliance requires and executing against it in real time is where risk accumulates.
Documentation failures, missed deadlines, inconsistent quality measurement, and incomplete audit trails carry concrete consequences: CMS sanctions, state regulatory fines, accreditation loss, payer contract penalties, and litigation exposure. Equally damaging and often underestimated is reputational harm. A single high-profile audit finding, a publicized denial overturned on appeal, or a pattern of prior authorization delays can erode member trust, attract media attention, and invite regulatory scrutiny that outlasts the original incident. In a landscape where organizations are held accountable not just for deliberate violations but for systemic failures they should have detected, the margin for unintended error is narrow.
The operational risk surface extends beyond regulatory and reputational exposure. Fragmented, manual compliance workflows create information security vulnerabilities that sophisticated threat actors actively exploit. A cyber-attack compounds compliance exposure directly: breach notification obligations trigger under HIPAA and state law, audit timelines are disrupted, submission deadlines are missed, and the remediation period itself becomes a window of heightened regulatory and reputational risk.
The structural failure driving these outcomes is architectural. Compliance logic lives in policy documents, training programs, and specialist teams and not in the systems that do the work. As a result, every manual hand-off, every inconsistently applied criterion, and every undocumented decision becomes a potential liability.
At Autonomize AI, we have spent years building AI agents that operate inside these workflows, not adjacent to them. What we have observed is that the organizations achieving durable compliance outcomes are not the ones with the largest compliance functions. They are the ones that have embedded compliance logic into the way work gets done. This paper reflects what we have learned across deployments serving some of the largest health enterprises in the country.
Accreditation Readiness: From Periodic Fire Drill to Continuous Protection
For NCQA and similar accreditation programs, the traditional model is retrospective. Teams mobilize weeks or months before a review, assembling documentation, reconciling inconsistencies, and validating that every file meets evaluator criteria. The cost is enormous in labor, in distraction from operational priorities, and in exposure. When preparation begins after the fact, documentation gaps that could have been addressed during normal operations become deficiencies that affect scores, trigger corrective action plans, or jeopardize accreditation status entirely.
Accreditation loss is not a theoretical outcome. It affects payer contracts, government program eligibility, and employer relationships. The reputational consequences from public reporting of accreditation failures as well as perception among members and referring providers compound the operational impact.
When AI agents are embedded into case processing workflows, accreditation readiness becomes a continuous condition rather than a periodic project. Documentation is validated against regulatory criteria as cases move through the system. Required data elements are enforced at the point of entry. Structured audit trails are generated as a natural byproduct of daily operations, not assembled retroactively under pressure.
The evidence is already there when it is needed. The scramble disappears not because the standards have changed, but because the operational system now produces compliant outputs by default, every day.
This shift changes the risk profile fundamentally. Organizations are no longer dependent on a review cycle catching documentation deficiencies before the accreditor does.
Clinical Quality: Closing the Gap Before It Becomes a Liability
Quality performance programs such as HEDIS, Stars, and value-based contracts depend on accurate abstraction of clinical data and precise alignment with measure logic. The traditional approach relies on manual chart abstraction: clinicians or certified abstractors reviewing records, identifying relevant data elements, and mapping them to measure specifications. It is slow, expensive, and inconsistent.
Inconsistency in quality measurement is itself a compliance and financial risk. Missed care gaps translate directly into lower Stars scores, reduced quality bonus payments, and contract penalties. In value-based arrangements, documentation failures can trigger recoupment demands or disqualify reported outcomes. Errors in HEDIS submissions, even unintentional ones, expose organizations to audit findings and, in some contexts, to allegations of data integrity failures with far-reaching consequences.
AI-driven abstraction changes the economics and the accuracy of this work. These are not just keyword-matching systems. Effective clinical abstraction engines interpret documentation in context, resolve ambiguity, and align findings to the specific logic required by each measure. The result is not just faster abstraction, it is more consistent abstraction across the full member population, with a defensible, documented methodology that withstands audit scrutiny.
The shift is from chasing charts after the fact to spotting quality gaps early, so issues can be fixed before they impact outcomes or finances.
Organizations that move to AI-assisted abstraction are not simply measuring quality faster. They are eliminating the compliance gap between what care was delivered and what the record can prove, and doing so before the window closes.
Clinical Workflows: Managing Compliance Under Time Pressure
Clinical workflows such as prior authorization and utilization management represent some of the highest-stakes compliance terrain in healthcare. Turnaround time requirements are strictly defined by regulation and contract. Documentation standards are exacting. The consequences of failure are immediate, measurable, and escalating.
CMS and state regulators have made prior authorization compliance a priority enforcement area. Systematic turnaround violations can result in civil monetary penalties, consent decrees, and corrective action plans. Beyond regulatory action, authorization failures that lead to delayed or denied care carry litigation exposure and the reputational risk of public reporting. A pattern of violations, once identified by CMS or a state insurance commissioner, rarely stays private.
High volumes, variable clinical documentation quality, and the need to apply nuanced medical criteria across thousands of cases per day create conditions where manual processes inevitably degrade: deadlines lapse, criteria are applied inconsistently, and escalation decisions go undocumented. Each failure point is a liability.
AI orchestration addresses this by operating continuously across the workflow. Turnaround clocks are monitored in real time. At-risk cases are escalated before deadlines lapse, not after. Every routing decision, every clinical criterion applied, and every exception pathway is logged, creating a defensibility layer that manual processes cannot replicate at scale.
The compliance benefit is inseparable from the operational benefit. When AI handles intake triage, documentation assembly, and criteria pre-screening, licensed clinical reviewers focus on the cases that require their judgment. Turnaround times improve not because the system is cutting corners, but because it is eliminating the administrative friction that consumes reviewer time and introduces error.
Regulatory Submissions: Eliminating Rejection Risk Before It Reaches the Regulator
The volume and complexity of regulatory reporting obligations facing healthcare organizations continues to expand, including CMS data submissions, state regulatory filings, payer-specific quality reports, and financial attestations. Each carries specific formatting requirements, validation rules, and hard deadlines, as well as a vector for operational error with real consequences.
Submission failures are rarely treated as minor administrative oversights. Rejected or late filings trigger rework cycles that consume staff time and delay compliance milestones. In some contexts, they carry direct financial penalties. Repeated failures attract heightened regulatory scrutiny. And in an environment where regulators are increasingly sophisticated about auditing submission data quality and not just submission timeliness, errors that make it through initial review can surface later as findings with retroactive implications.
AI-powered workflows address this by standardizing the data extraction, conversion, and validation stages of the reporting pipeline. Automated pre-submission checks catch formatting errors, missing fields, and logical inconsistencies before they reach the regulator. The goal is to make rejection a rare exception rather than a recurring operational tax and to ensure that when data is submitted, it reflects an accurate report-ready underlying record.
Audit Readiness: An Architectural Property, Not a Periodic Event
Audit readiness, whether for internal reviews or external regulatory exams, is typically treated as a project. Teams pull records, reconcile documentation, assemble evidence packages, and hope the sample holds.
This model is fragile. It rests on the assumption that normal-course operations produce audit-ready documentation. In practice, they usually do not. Documentation gaps, inconsistent formatting, missing timestamps, and incomplete decision records are discovered only when someone goes looking. By then, the cost of remediation is high, and the credibility cost may be higher. When auditors discover documentation gaps that an organization should have detected internally, the finding implicates not just the specific record but the adequacy of the organization’s compliance infrastructure overall. That perception shapes how regulators approach future oversight.
When AI is embedded into operational workflows, audit trails are produced by default. Every decision, routing action, escalation, and document version is logged with full traceability. Internal audit teams can query this data continuously, identifying anomalies before they become findings. External auditors receive structured, consistent evidence packages rather than manually assembled binders with variable quality.
Audit readiness is not something organizations prepare for; it is an architectural property of a well-designed operational system.
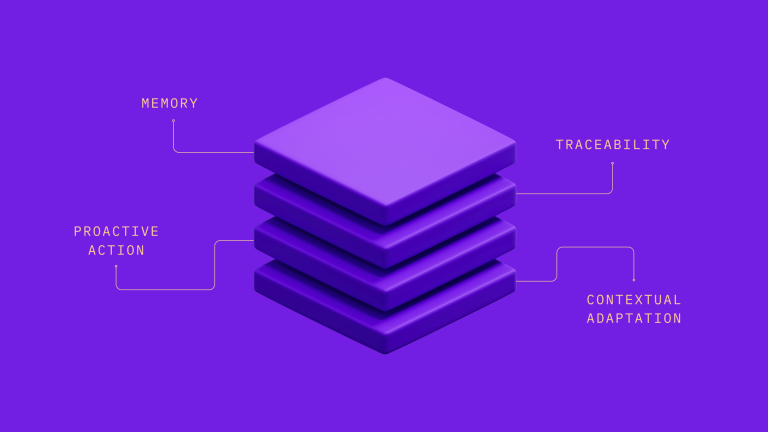
The Risk-Benefit Architecture: What Makes This Work
The common thread across each of these domains is architectural. AI is not applied at the margins as a point solution for one function. It is embedded into the operational backbone: intake, routing, review preparation, documentation, escalation, and reporting. That integration is what converts AI from a productivity tool into a compliance infrastructure. This is the critical distinction. Building compliance logic into the architecture of how work gets done does not simply add one layer of protection across one workflow; it produces compounding benefits across every workflow it touches. A documentation standard enforced at intake improves accreditation readiness, reduces prior authorization audit exposure, strengthens regulatory submission quality, and narrows the information security attack surface simultaneously. A structured audit trail generated in the utilization management workflow supports internal audit, answers external regulator inquiries, and provides the evidence base for quality measure submissions, all from a single operational action. Each capability reinforces every other: the whole is substantially greater than the sum of its parts, and the return on architectural investment compounds over time.
The table below maps the conventional approach and its associated risks against the protections that architecturally integrated AI provides:
| Conventional Approach and Its Risks | Architecturally Integrated AI and Its Protections |
| Retrospective documentation → discovered gaps trigger penalties | Continuous real-time documentation → gaps caught before they become violations |
| Manual chart abstraction → inconsistency creates audit exposure | AI-driven extraction aligned to measure logic → consistent, defensible record at scale |
| Periodic audit preparation → scramble reveals undocumented decisions | Audit trails produced as operational byproduct → evidence inherent in every workflow |
| Reactive escalation after deadline lapse → regulatory citations, fines | Proactive monitoring with risk-based escalation → deadlines met, liability avoided |
| Siloed compliance across functions → structural blind spots | Unified compliance architecture → no gaps between systems or teams |
| Evidence assembled for auditors on demand → variable quality, credibility risk | Evidence inherent in the operational record → structured, consistent, defensible |
| Fragmented manual workflows and unstructured repositories → expanded cyber threat attack surface (ransomware, exfiltration, breach) | Consolidated, governed data flows → reduced information security exposure and breach notification risk |
This distinction determines whether compliance improvements are sustainable. Point solutions can improve one metric in one cycle. Architectural integration changes how the organization operates, permanently reducing variability, eliminating manual rework at the source, and closing the structural gaps through which penalties, sanctions, and reputational harm enter.
Governance and Accountable Autonomy
None of this works without governance. Every AI deployment should incorporate defined oversight structures, human-in-the-loop safeguards, and clear boundaries on what AI decides versus what it recommends. Clinical decision authority remains with licensed professionals. AI systems flag ambiguity, escalate edge cases, and document decision pathways, but they do not replace the judgment that regulatory frameworks require to be exercised by qualified individuals.
We describe this as accountable autonomy. AI operates within governed parameters with transparent reasoning, complete audit trails, and defined escalation protocols. This is not a feature added for enterprise procurement. It is foundational design: the architecture of a system that can be examined, explained, and defended.
Every AI action is logged. Every escalation is traceable. Every clinical override is documented. This level of transparency is what enables organizations to deploy AI at scale while maintaining the oversight that regulators, accreditors, and their own compliance and audit teams require. And, it ensures that when a regulator or auditor asks how a decision was made, the answer is available, complete, and consistent with the decision criteria that were supposed to apply.
The Strategic Imperative
The healthcare organizations pulling ahead in compliance aren’t the ones with the biggest teams or the most refined manual workflows. They’re the ones that have embraced a fundamental shift: compliance has to be built into how work happens, not layered on after the fact.
The risk of staying manual is no longer abstract; it compounds with every cycle. Fragile documentation, judgment-based escalations, and hand-built submissions quietly accumulate exposure across audits, prior authorization, and quality reporting. At the same time, regulatory scrutiny is only intensifying, and what used to be operational inefficiency is now translating directly into higher error rates, rising remediation costs, and growing reputational risk. That exposure is no longer limited to compliance alone; it now extends into security. Fragmented, manual processes expand the attack surface for threats like ransomware and data breaches, each carrying their own regulatory and public consequences.
The path forward is structural. By embedding regulatory logic, quality measures, audit trails, and escalation protocols directly into the systems executing the work, organizations reduce risk at its source, shifting compliance from a reactive function to a built-in capability.